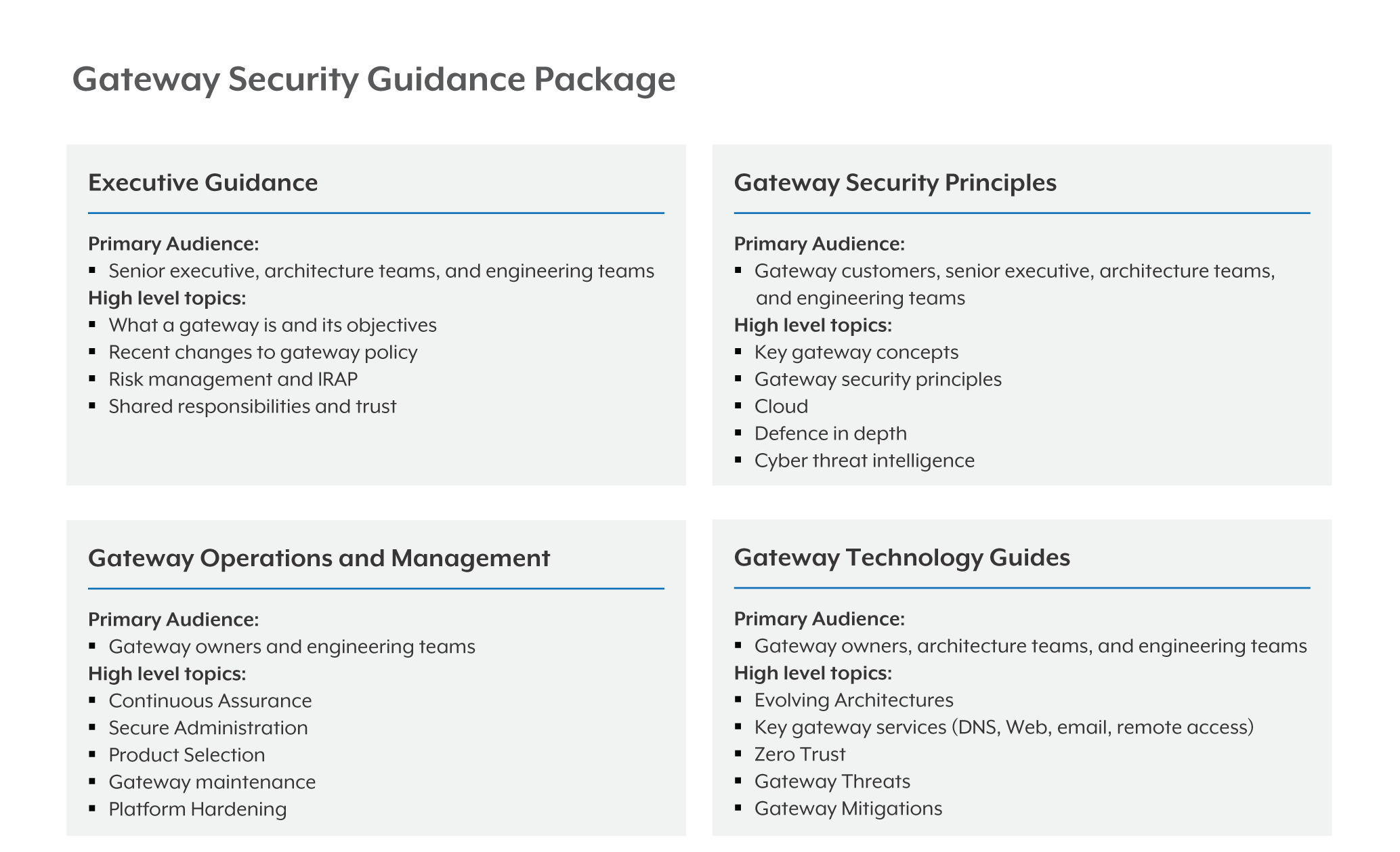
- Gateway security guidance package: Overview (this guide) is for all audiences before reading other guides in the package.
- Gateway security guidance package: Executive guidance is for senior or executive decision-makers who are accountable for designing, procuring, operating, maintaining or disposing of gateway solutions.
- Gateway security guidance package: Gateway security principles is for security, architecture and engineering teams who are responsible for designing or operating gateway solutions in their organisation
- Gateway security guidance package: Gateway operations and management is for engineering, operations and support teams to understand better-practice approaches for operating, maintaining and disposing of gateways
- Gateway security guidance package: Gateway technology guides is for security, architecture, engineering, operations and support teams and provides detailed guidance on key technical concepts referred to throughout the Gateway Guidance package.
¶ Policy and other considerations
The Gateway Security Guidance package should not be considered government policy or a checklist. ASD recommends organisations assess their gateways against their obligations under the PSPF, specifically as they relate to risk management (ISO 31000), ICT risk management (ISO 27001), the Public Governance, Performance and Accountability Act 2013 (PGPA Act), the Commonwealth Procurement Rules, and the guidance within the Information Security Manual(ISM) and the Department of Home Affairs' PSPF, especially Policy 11.
NCEs should use the results of gateway IRAP assessments to inform their authorisation to operate decisions.
Entities must also refer to the Digital Transformation Agencies (DTA’s) gateway policy when procuring internet-facing gateway services.
Commonwealth entities seeking to procure gateway services must consider the DTA’s Hosting Certification Framework (HCF) and ensure all sensitive and classified government data and associated infrastructure is hosted by a certified provider. The framework provides a process for government customers to attest to the risks of using a service.
¶ Gateway Security Guidance Package: Executive Guidance
The purpose of this guidance is to inform decision-makers at the executive level of their responsibilities, the appropriate considerations needed to make informed risk-based decisions, and to meet policy obligations when leading the design or consumption of their organisation's gateway services.
¶ Gateway Security Guidance Package: Gateway Security Principles
This guidance is one part of a package of documents that forms the Australian Signals Directorate (ASD)'s Gateway Security Guidance package written for audiences responsible for the procurement, operation and management of gateways.
¶ Gateway Security Guidance Package: Gateway Operations and Management
This guidance is one part of a package of documents that forms the Australian Signals Directorate (ASD)'s Gateway Security Guidance package written for audiences responsible for the operation and management of gateways.
¶ Gateway Security Guidance Package: Gateway Technology Guides
This guidance is one part of a package of documents that forms the Gateway Security Guidance package. When designing, procuring, operating, maintaining or disposing of a gateway, it is important to consider all the documents from the Gateway Security Guidance package at different stages of governance, design and implementation, and not to consume this guidance in isolation.