10 September 2025 - cached from https://www.mallesons.com/au/en/insights/latest-thinking/the-protective-security-policy-framework-has-been-updated-whats-new.html
The Department of Home Affairs published the 2025 Annual Release of the Protective Security Policy Framework on 24 July 2025 (PSPF 2025). This is more than an annual update—PSPF 2025 embeds Zero Trust principles, increases visibility of technology assets, and integrates ASD collaboration into the core of protective security. It also features an emphasis on keeping up-to-speed with emerging technologies, with new material on Artificial Intelligence (AI), cloud-based gateway capabilities, and post-quantum encryption.
PSPF Requirements are mandatory for non-corporate Commonwealth entities (i.e. most departments and agencies) and extend in practice to most contractors and suppliers handling Commonwealth data. Organisations interacting with the Commonwealth should conduct a gap analysis against the new requirements (including in respect of Gateways/SSEs, hosting certification, and Technology Asset Stocktakes) and update contract templates and guides to ensure PSPF obligations and associated resourcing are addressed before the next reporting and procurement cycles.
PSPF 2025 forms part of tranche 2 of the Commonwealth Cyber Security Uplift reforms, which are in turn part of a broader push towards progressing the 2023-2030 Australian Cyber Security Strategy. The strategy aims to make Australia one of the world’s most cyber secure nations by 2030, so we expect to see more changes on the way – starting with the Hosting Certification Framework (reforms to which are currently open for consultation).
Read on for a refresher of how the PSPF fits together, why it’s relevant (even outside of government) and a high-level summary of what else is new in PSPF 2025.
Technology takes centre stage: how the updates map across security domains
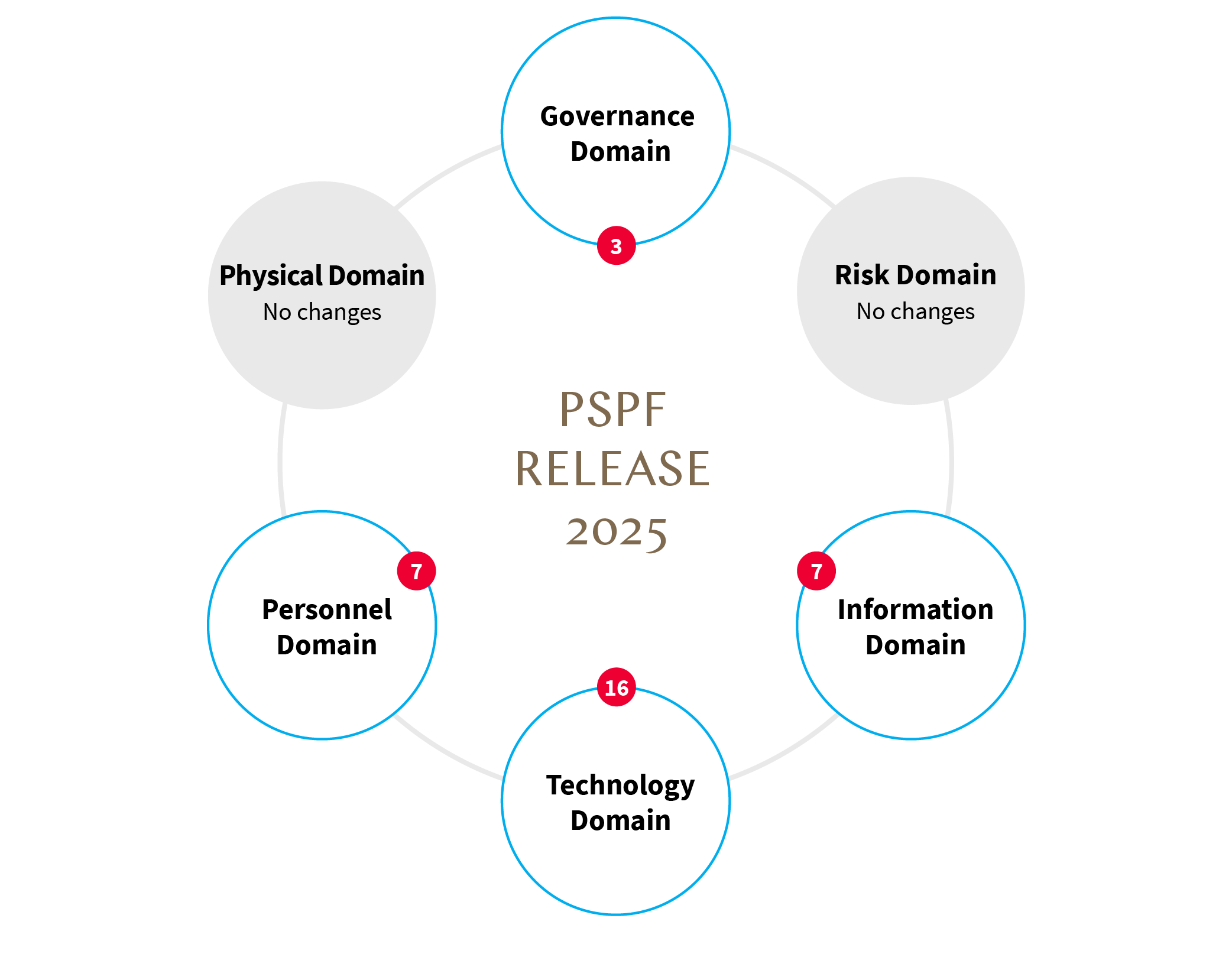
The PSPF is organised into 6 security ‘domains’ (governance, risk, information, technology, personnel and physical). The technology domain has taken centre stage in this year’s release with 16 updates to policy content and PSPF Requirements[1] including:
- new sections and requirements related to AI, post-quantum cryptography, connected peripheral technologies and embedding ‘Zero Trust Culture’,
- uplifts in requirements related to gateway security (including a new Gateway Security Standard) and technology asset management,
- the introduction of ASD’s Cyber Security Partnership Program and Cyber Threat Intelligence Sharing Platform, and
- a new standard for declared Systems of Government Significance.
How to find your way around (and why you need to)
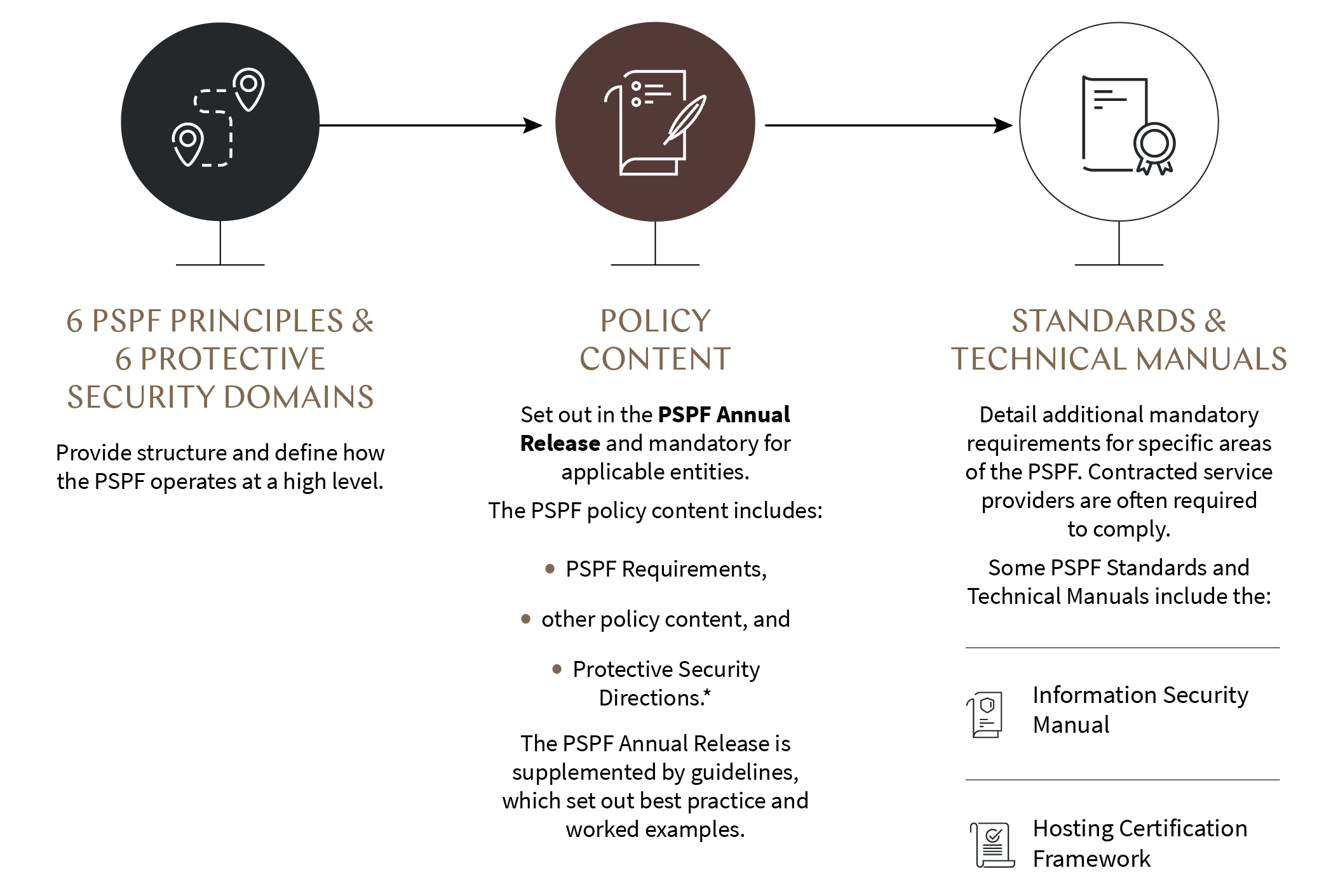
The PSPF is a designed to be a modular framework. At its apex sit 6 principles (the PSPF Principles) which set the tone for a risk-based, proactive approach to protective security. Those principles are distilled into the six security domains and a suite of government policy documents, including the annual PSPF release and the requirements contained within.
Beneath the PSPF requirements sit PSPF Standards, such as the new Gateway Security Standard, and a suite of Technical Manuals maintained by specialist agencies (including ASIO, ASD and Defence). Standards and Technical Manuals operate at a more granular level of detail and are the technical backbone of the PSPF. Finally, guidelines provide case studies and recommended approaches to help entities calibrate controls to their threat environment.
TLDR; the architecture moves from the strategic (Principles) to the operational (Standards, Technical Manuals), giving the Commonwealth a menu of controls that can be scaled according to business impact and operational context.
*Directions made by the Secretary for Home Affairs which non-corporate Commonwealth entities must comply with. For example, PSPF Direction 001-2025 (made in February this year) prevents the access, use or installation of, and requires the removal of existing, DeepSeek products, applications and web services.
The PSPF is Australian Government policy, meaning compliance is mandatory for all non-corporate Commonwealth entities. Corporate Commonwealth entities and wholly-owned Commonwealth companies are expected to treat the framework as better practice. State and territory agencies are required to apply the PSPF when holding and/or accessing Commonwealth-classified material in accordance with arrangements agreed between the Commonwealth and the relevant state or territory.
Not in government? The PSPF could still apply
Critically for the private sector, any service provider—whether cloud host, financial advisor, facilities manager or recruitment firm—must implement the relevant PSPF controls where this is required by contract, deed, panel head-agreement or direction. These controls commonly flow through the Digital Transformation Agency’s Hosting Certification Framework, the Defence Security Principles Framework, IRAP-assessed cloud terms and the “minimum secure” clauses and specifications now appearing in RFTs across Government (i.e. requirements to apply the relevant security measures outlined in the PSPF, or associated Standards and Technical Manuals such as the Information Security Manual, as a minimum standard).
If you process, store, transmit or can influence the protection of Commonwealth information or assets, you will need to map your controls to the PSPF, and keep them updated accordingly.
PSPF 2025: The lay of the land
1. Technology domain
To keep pace with the emerging digital landscape, PSPF 2025 introduces new policy content on AI, quantum computing, and connected peripheral technologies. Other key changes include an uplift to Gateway security requirements and the requirement to conduct a stocktake of all internet-facing systems and services.
|
NEW ARTIFICIAL INTELLIGENCE (AI) New policy content and clarification on which PSPF Requirements apply [2]
|
|
NEW QUANTUM COMPUTING AND CRYPTOGRAPHY New PSPF Requirement for newly procured cryptographic equipment –
|
|
NEW CONNECTED PERIPHERAL TECHNOLOGIES[6] New policy content on minimising risk – Entities should adopt strategies to minimise their exposure to the risks posed by connected peripheral technologies and educating their personnel on the potential vectors of compromise.[7] |
|
NEW ZERO TRUST CULTURE AND CYBER SECURITY STRATEGY New Guiding Principles to Embed a Zero Trust Culture (Guiding Principles) and more regular reporting –
|
|
NEW TECHNOLOGY ESTATE Entities now required to create Technology Asset Stocktake and Technology Security Risk Management Plan -
|
|
NEW CYBER SECURITY PARTNERSHIP PROGRAM New Cyber Security Partnership Program – Entities are required to participate in the Cyber Security Partnership Program run by the Australian Signals Directorate (ASD) and notify the ASD if their risk profiles change.[12] The program is also available to other organisations, and aims to provide threat information, news, advice, collaboration opportunities, and resilience building activities.[13] |
|
NEW CYBER THREAT INTELLIGENCE SHARING PLATFORM Entities are now required to connect to ASD’s Cyber Threat Intelligence Sharing Platform –[14] ASD’s Cyber Threat Intelligence Sharing (CTIS) platform is a two-way sharing platform that enables government and industry partners to receive and share information about malicious cyber activity. Entities are strongly encouraged to share data and the malicious indicators of compromise or sightings with ASD.[15] |
|
NEW SYSTEMS OF GOVERNMENT SIGNIFICANCE New Systems of Government Significance (SoGS) Standard -[16]
|
|
NEW GATEWAY SECURITY (REPLACES INTERNET GATEWAY POLICY) Internet Gateway Policy retired, replaced with Gateway Security Standard and updated PSPF Requirements -[17]
|
|
UPLIFT AUSTRALIAN GOVERNMENT HOSTING CERTIFICATION FRAMEWORK Expanded requirement to use certified providers – Certified Cloud Service Providers and Data Centre Providers must now be used for all security classified or SoGS information and data. |
2. Governance domain
A key update in the governance domain is the expanded focus on foreign ownership, control or influence (FOCI) risks. Entities are now required to report potential or identified FOCI risks discovered during procurement processes to the Department of Home Affairs as soon as possible and include these risks in their annual PSPF reporting. PSPF 2025 also features increased accountability and more frequent reporting for CISOs.
|
UPLIFT CHIEF INFORMATION SECURITY OFFICER (CISO) Increased scope and accountability — the CISO is now:[22]
The CISO must also report on the entity’s cyber security risk at each meeting of the Audit Committee and biannually on the progress of the cyber security strategy and uplift plan.[23] |
|
UPLIFT REPORTING - SIGNIFICANT SECURITY INCIDENTS Risk of foreign ownership, control or influence — [24]
|
3. Information domain
Information policy changes are practical but significant: security caveats can now be applied to any classification, disposal options for physical information have expanded, and new rules on international travel with SECRET material and sharing AUSTEO information represent notable shifts in how sensitive data can be handled and exchanged.
|
UPLIFT SECURITY CAVEATS Security caveats (e.g. AUSTEO, CABINET or EXCLUSIVE-FOR) can appear in conjunction with any security classification – In previous releases of the PSPF, security caveats could only appear in conjunction with a security classification of PROTECTED or higher.[25] |
|
UPLIFT INTERNATIONAL TRAVEL WITH PHYSICAL INFORMATION SECRET information is carry-on only — Travelling with physical information classified as SECRET overseas is not recommend. If required, the information must be transported as carry-on in a diplomatic bag and remain in the custody of an Australian Diplomatic or Australian Official passport holder. If carry-on is not permitted, travel should not proceed.[26] |
|
DISPOSING OF PHYSICAL INFORMATION More ways to dispose of physical information — Physical information classified as PROTECTED, SECRET and TOP SECRET can now be disposed of using ASIO-T4 approved document destruction methods (in addition to Class A and B shredders, as applicable).[27] Note that disposal of TOP SECRET information still needs to be documented and witnessed.[28] |
|
NEW EXCEPTION SHARING WITH NON-GOVERNMENT STAKEHOLDERS New exception to Requirement 0077 — Entities are no longer required to agree handling requirements and protections with non-government stakeholders before sharing security classified information or resources where:
|
|
NEW EXCEPTION SHARING AUSTEO INFORMATION New exemptions process for sharing AUSTEO information with non-citizens —
|
4. Personnel domain
The changes in the Personnel domain emphasise speed and clarity: there are now explicit rules prohibiting dual eligibility waivers, shorter timeframes for APS employees to seek internal review of vetting decisions, and clear limits on temporary access to classified information—requiring sponsors to tighten onboarding and clearance maintenance processes.
|
ELIGIBILITY WAIVERS Clarification on eligibility waivers —
|
|
SHORTER TIMEFRAME FOR APS EMPLOYEES REVIEW OF DECISIONS APS employees have less time to seek internal review of vetting decisions — APS employees now have 60 days to seek internal review of a vetting decisions by the relevant vetting agency (rather than 120). Non-APS employees do not necessarily have access to internal review, but can lodge a complaint with the Commonwealth Ombudsman.[33] |
|
AUSTRALIAN OFFICIALS AND OFFICE HOLDERS Name change and new policy content for Commonwealth Officials — Section 20 of the PSPF (now with a new name) introduces new policy content on the security risks facing Australian officials and other office holders (e.g. high office holders, statutory office holders, Special Envoys, Royal Commissioners and Judges).[34] |
What to take home…
PSPF 2025 is not a walk in the park, but it’s important that organisations interacting with the Australian Government assess their compliance posture and contracts against the new PSPF requirements. Non-conformance will increasingly determine tender success, service continuity and risk exposure as Government implements the Commonwealth Cyber Security Uplift reforms and 2023-2030 Australian Cyber Security Strategy.
With the Hosting Certification Framework currently open for consultation, and more reform on the way, we will continue to monitor developments and share our insights.
Key documents
This summary is not a substitute for reading the full PSPF 2025 release. You can find the full release and supporting documents on the Department of Home Affairs’ website, here.
Want to dive deeper? Other key PSPF documents include:
- the PSPF Guidelines 2025 (published alongside the PSPF Annual Release on 24 July 2025),
- the Information Security Manual (last updated June 2025),
- the Hosting Certification Framework (last updated March 2021, currently under reform), and
- the new Australian Government Gateway Security Standard (released 24 July 2025).